.png)
.png)
• Aug 28, 2025: Bitnami’s free catalog narrows to a limited, hardened subset that’s “latest” only. Most versioned tags move out of the free tier.
• Brownouts (10 images unavailable for 24h each) to surface hidden pulls: Aug 28–29, Sept 2–3, Sept 17–18.
• Public catalog deletion is planned for Sept 29, 2025: Prepare now: repoint, mirror, test during brownouts, and put guardrails in place.
• Use Chkk CLI to identify all Bitnami images in your environment facing deprecation risk. Run chkk bitnami to get started and find alternative images. No login or install required, free to use.
Bitnami is a popular open-source project that provides pre-packaged, ready-to-use application containers, Helm charts, and virtual machine images. It simplifies the deployment of complex software stacks by maintaining curated, secure, and easy-to-consume builds for Kubernetes, Docker, and cloud platforms.
Bitnami is fundamentally altering the availability and maintenance of its container images and Helm charts. This move is tied to Broadcom’s shift towards a paid "Bitnami Secure" subscription model.
Here's a breakdown of the critical changes:
bitnami to a Split Catalog: Bitnami is moving away from freely available images under the Docker Hub username bitnami. Instead, images will be split into two main categories: docker.io/bitnamisecure: This repository lists the free, hardened community images (latest-only). The full commercial catalog is delivered via private registries with a Bitnami Secure Images subscription.docker.io/bitnamilegacy: Most existing container images, including older or versioned tags (e.g., postgresql:13.7.0), will be moved to this legacy repository. Crucially, images in this repository will receive no further updates, fixes, or support and are intended only for temporary migration purposes.docker.io/bitnami Repository: After August 28th, the main Bitnami Docker Hub repository will only contain the limited community-tier subset of hardened images, exclusively with "latest" tags.docker.io/bitnamicharts will stop receiving updates.postgresql:13.7.0 or redis:7.0.5, you will effectively lose access to them in the free tier, being left with "latest" tags or the unsupported legacy repo.bitnamilegacy.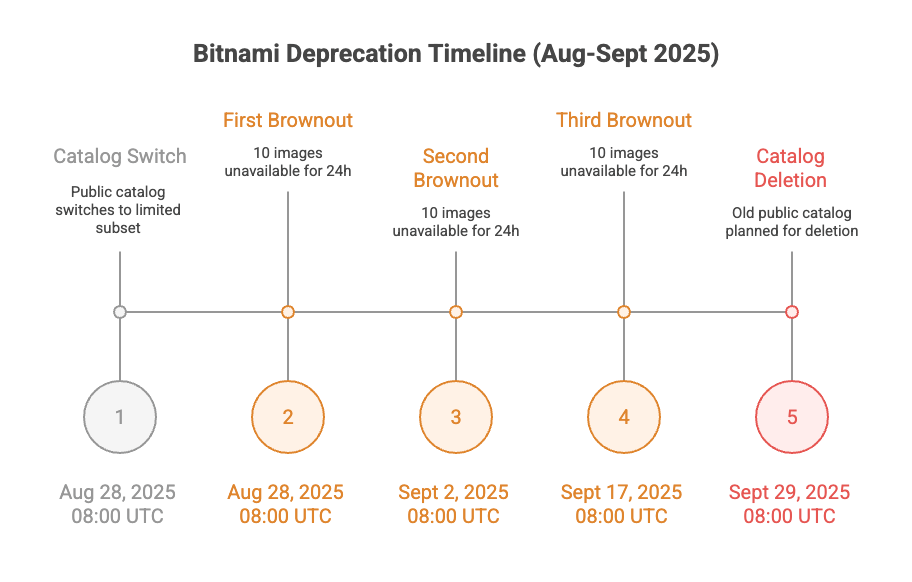
Use these windows to validate cluster readiness and surface any hidden pulls.
docker.io/bitnami after the deadline will likely hit ErrImagePull / ImagePullBackOff.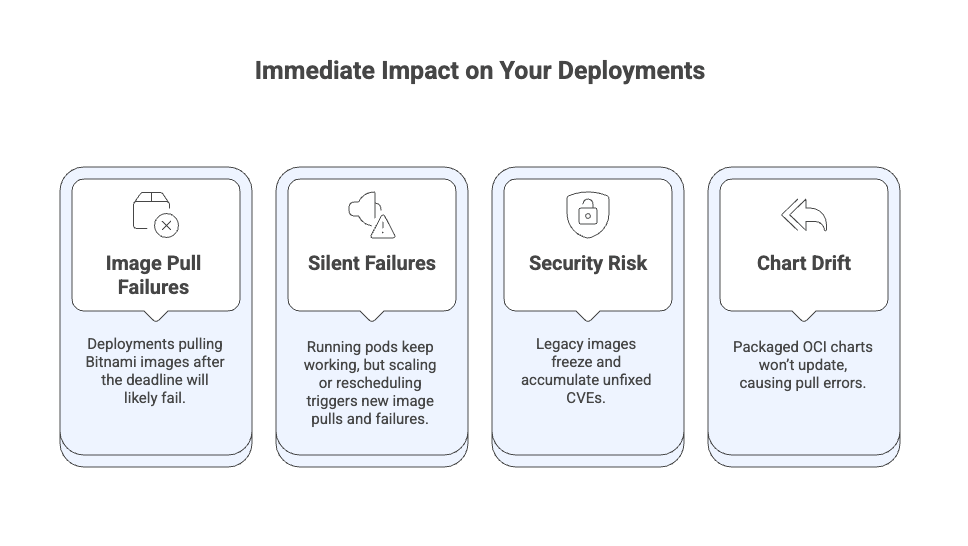
Your deployments will eventually fail. You might not see an immediate explosion on that exact day, but the next time Kubernetes tries to pull a Bitnami image that isn’t in the new limited set, it won’t find it – resulting in ImagePullBackOff or ErrImagePull errors.
kubectl get pods --all-namespaces -o jsonpath='{.items[*].spec.containers[*].image}' | grep bitnamihelm list --all-namespacesdocker.io/bitnami images.bitnamilegacy (Temporary Workaround)values.yaml files or use --set flags during helm upgrade to point to the bitnamilegacy repository.bitnamisecure first: Before defaulting to bitnamilegacy, verify if your specific application is one of the few that will receive updated images in bitnamisecure. Note that these are typically "latest" tags and often intended for development only.Use the scheduled brownouts to simulate downtime and confirm that CI/CD, autoscaling, and rescheduling don’t break with your new image sources.
docker.io/bitnamilegacy (Know the Risks)Using Bitnami Legacy can prevent immediate breakage, but it does not receive security updates or fixes; Bitnami also notes it’s not planned to be kept around for long. Mirror anything you need and move to a supported path.
Yes. Source code for Helm charts remains OSS on GitHub. Packaged OCI charts in docker.io/bitnamicharts remain available but stop receiving updates after Aug 28, 2025; you must override bundled image repositories to valid ones (e.g., Legacy or Secure).
On AWS Marketplace it’s $6,000/month for a 12‑month term.
Yes: Sealed Secrets, charts‑syncer, and minideb continue on docker.io/bitnami without change.
Use charts‑syncer to relocate OCI charts and rewrite image locations; Bitnami provides this tool openly.
The community is actively debating new charts and migration strategies—there’s no consensus yet. In the meantime, you should lock down your plan: inventory all Bitnami usage, repoint or mirror critical images, test during brownouts, and enforce registry policies to prevent regressions. Set dates, communicate the change, and track official updates so new pulls don’t turn into ImagePullBackOff on the wrong day.
1. Download Chkk CLI - free, no-login or install required to use Bitnami Alternatives Finder
2. Run chkk bitnami command.
3. Discover all Bitnami images in your cluster at risk of deprecation, and review recommended alternatives.